关于为用户启用密钥扫描警报
您可以为拥有的任何免费公共代码库启用用户的密钥扫描警报。
如果您是组织所有者,则可以使用安全配置一次启用多个代码库的密钥扫描。 有关更多信息,请参阅“关于大规模启用安全功能”。
为用户启用密钥扫描警报
-
在 GitHub 上,导航到代码库的主页。
-
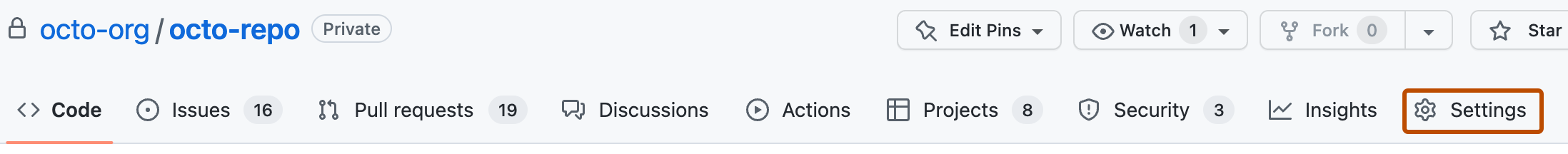
在您的代码库名称下,单击 设置。如果您看不到“设置”选项卡,请选择下拉菜单,然后单击设置。
-
在侧边栏的“安全”部分,单击 代码安全和分析。
-
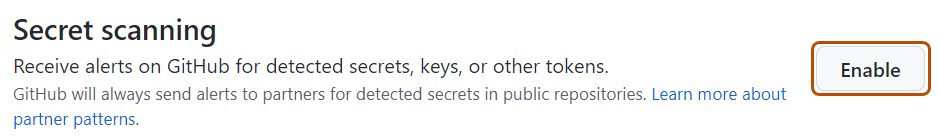
滚动到页面底部,然后单击密钥扫描的启用。如果您看到禁用按钮,则表示密钥扫描已为该代码库启用。
代码库管理员可以随时选择禁用代码库的密钥扫描。 有关更多信息,请参阅“管理代码库的安全和分析设置”。
后续步骤
- “查看和筛选密钥扫描警报”
- “关于密钥扫描警报”